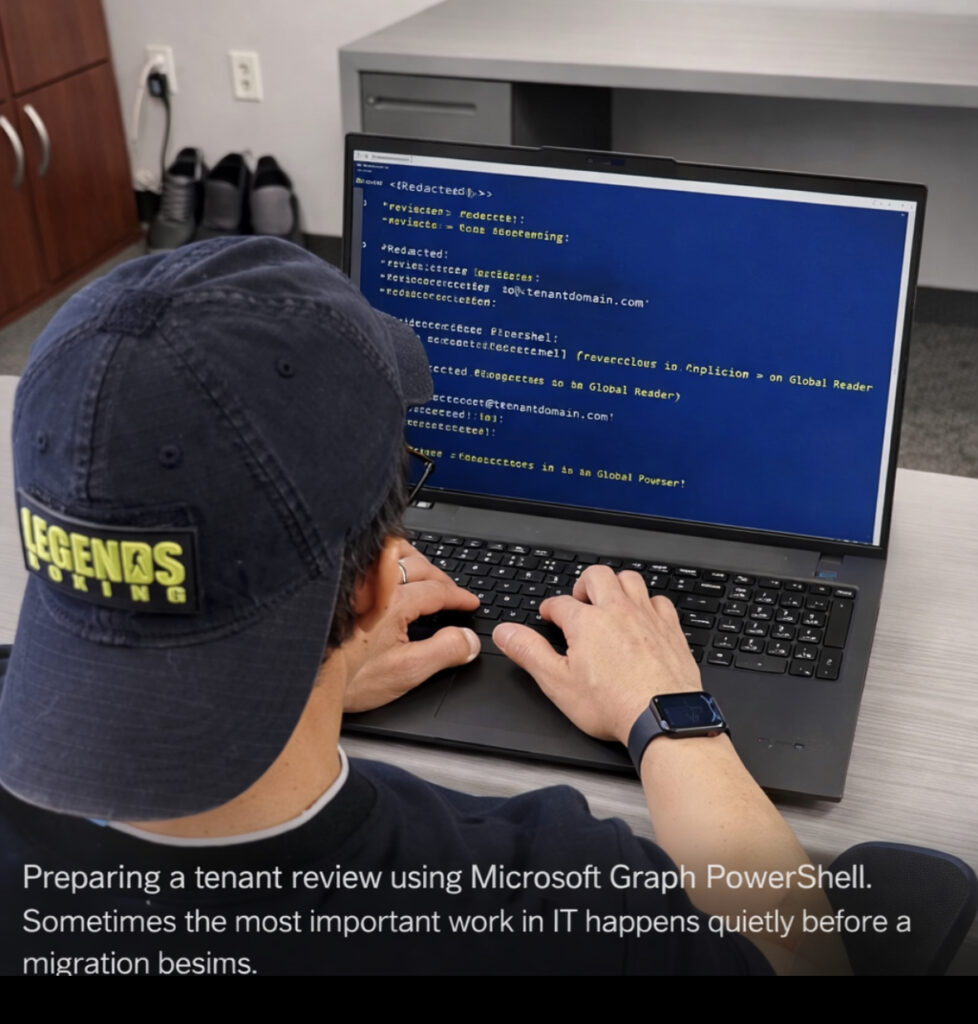
During Microsoft 365 tenant reviews or migration preparation, it is common to create a temporary read-only account so engineers can safely inspect the environment.
Instead of granting administrative permissions, the recommended approach is to assign the Global Reader role. This role provides visibility into configuration, policies, and identity structure while preventing any changes to production resources.
This method is frequently used during tenant consolidation, acquisitions, or domain transitions where a review of the existing environment is required before cutover.
The following PowerShell example demonstrates how to create a temporary user and assign the Global Reader role using Microsoft Graph PowerShell.
1. Create the Entra Account
Creates a temporary user account for tenant inspection.
$PasswordProfile = @{
Password = "<ExamplePassword>"
ForceChangePasswordNextSignIn = $false
}
New-MgUser `
-DisplayName "Tenant Review Account" `
-UserPrincipalName "[email protected]" `
-MailNickname "reviewaccount" `
-AccountEnabled:$true `
-PasswordProfile $PasswordProfile2. Retrieve the Global Reader Role
Checks whether the Global Reader role is already active in the tenant.
$role = Get-MgDirectoryRole | Where-Object {$_.DisplayName -eq "Global Reader"}3. Activate the Role if Needed
Some roles are not active until they are first used.
$template = Get-MgDirectoryRoleTemplate |
Where-Object {$_.DisplayName -eq "Global Reader"}
New-MgDirectoryRole -RoleTemplateId $template.Id
$role = Get-MgDirectoryRole |
Where-Object {$_.DisplayName -eq "Global Reader"}5. Verify the Role Assignment
Get-MgDirectoryRoleMember -DirectoryRoleId $role.IdWhy This Approach Is Used
Providing a temporary Global Reader account allows migration engineers to review the tenant safely. The role grants visibility into identity, security policies, and configuration without allowing any changes.
This approach reduces risk while ensuring the incoming team can properly analyze the environment before migration activities begin.
© 2012–2026 Jet Mariano. All rights reserved.
For usage terms, please see the Legal Disclaimer.