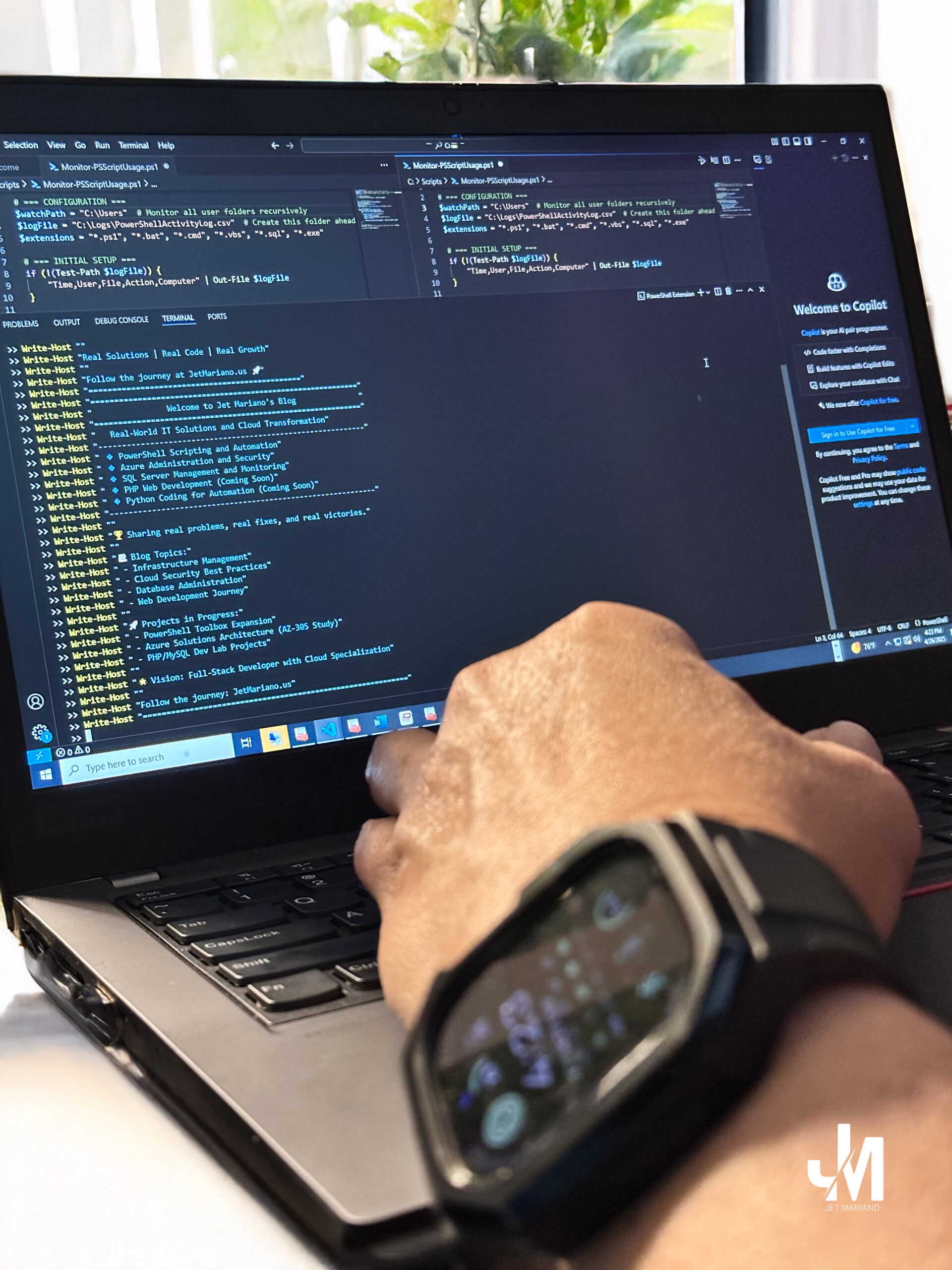
PowerShell is a powerful tool for IT professionals, allowing automation, troubleshooting, and system management.
Whether you’re handling system cleanup, retrieving Wi-Fi passwords, or managing processes, these PowerShell commands can be lifesavers.
Here are five must-know PowerShell scripts to add to your IT arsenal.
1. Extract All Installed Applications (For Inventory & Troubleshooting)
Need to check what software is installed on a system? This script pulls a list of all installed applications along with their version, publisher, and installation date.
Get-ItemProperty HKLM:\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\* |
Select-Object DisplayName, DisplayVersion, Publisher, InstallDate |
Sort-Object DisplayName |
Format-Table -AutoSize
🔹 Bonus: Export the list to a CSV file for documentation:
Get-ItemProperty HKLM:\Software\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\* |
Select-Object DisplayName, DisplayVersion, Publisher, InstallDate |
Export-Csv -Path "C:\InstalledApps.csv" -NoTypeInformation
2. Find and Kill Stubborn Processes
Have an unresponsive application? Use this script to forcefully close any running process by name.
$processName = "Teams" # Change this to the process you want to kill
Get-Process -Name $processName -ErrorAction SilentlyContinue | Stop-Process -Force
🔹 Bonus: Convert it into a user-friendly GUI:
Add-Type -TypeDefinition @"
using System;
using System.Windows.Forms;
public class KillProcess {
public static void Main() {
string processName = Microsoft.VisualBasic.Interaction.InputBox("Enter process name to kill:", "Kill Process", "Teams");
if (!string.IsNullOrEmpty(processName)) {
System.Diagnostics.Process[] procs = System.Diagnostics.Process.GetProcessesByName(processName);
foreach (var proc in procs) {
proc.Kill();
}
}
}
}
"@ -Language CSharp
[KillProcess]::Main()
3. Automate System Cleanup (Cache, Temp Files, Event Logs)
Over time, systems accumulate temporary files that can slow them down. This command clears temporary files, cache, and event logs:
Write-Host "Clearing Temp Files, Cache, and Event Logs..." -ForegroundColor Green
Remove-Item -Path "$env:TEMP\*" -Recurse -Force -ErrorAction SilentlyContinue
Remove-Item -Path "C:\Windows\Temp\*" -Recurse -Force -ErrorAction SilentlyContinue
Clear-EventLog -LogName Application, System, Security
Write-Host "Cleanup Completed!" -ForegroundColor Cyan
🔹 Bonus: Automate this cleanup by scheduling it in Task Scheduler.
4. Retrieve Wi-Fi Passwords Saved on a PC
Need to recover a saved Wi-Fi password? This script extracts the stored credentials for all previously connected networks:
(netsh wlan show profile) | Select-String "\:(.+)$" | ForEach-Object {
$network = $_.Matches.Groups[1].Value.Trim()
$password = (netsh wlan show profile name="$network" key=clear) | Select-String "Key Content\W+\:(.+)$"
if ($password) {
Write-Host "Wi-Fi: $network | Password: $($password.Matches.Groups[1].Value.Trim())" -ForegroundColor Green
}
}
🔹 Use Case: If you’re connected to a Wi-Fi network but forgot the password, this script retrieves it instantly.
5. Scan for Suspicious File Modifications (Forensic Command)
This script performs a recursive scan on a target machine to find recently modified files with specific extensions and flag any that contain high-risk keywords. Ideal for forensic scenarios.
$target = "RemoteComputerName" # Replace with computer name or IP
$extensions = @("*.ps1", "*.sql", "*.dll", "*.cs", "*.sln", "*.vbproj")
$keywords = 'drop', 'truncate', 'remove', 'shutdown'
$session = New-PSSession -ComputerName $target -ErrorAction SilentlyContinue
if ($session) {
Invoke-Command -Session $session -ScriptBlock {
param($exts, $keywords)
Get-ChildItem -Path "C:\" -Recurse -Include $exts -ErrorAction SilentlyContinue |
Where-Object {
$_.LastWriteTime -gt (Get-Date).AddDays(-90) -and
($_ | Select-String -Pattern ($keywords -join '|') -SimpleMatch -Quiet)
} |
Select-Object FullName, LastWriteTime, Length
} -ArgumentList $extensions, $keywords | Export-Csv -Path "$env:USERPROFILE\Desktop\forensic-scan.csv" -NoTypeInformation
Remove-PSSession $session
} else {
Write-Host "Unable to connect to $target"
}
Why it matters: This script was used during a forensic investigation while I was serving on a local government IT forensic team. Its purpose was to detect whether sensitive scripts or source code had been created, modified, or concealed on a colleague’s machine. By targeting specific file types and high-risk keywords (e.g., drop, truncate, remove, shutdown), the script helps identify signs of unauthorized automation, code tampering, or mismanagement of critical systems. It supported an internal review when key files were missing and operational stability was in question.
6. Quick System Resource Snapshot
# Display top 10 processes by CPU usage
Get-Process | Sort CPU -Descending | Select -First 10
# Show current CPU usage
Get-Counter '\Processor(_Total)\% Processor Time'
# Show available memory
Get-Counter '\Memory\Available MBytes'
# Summarize total, free, and used memory
Get-WmiObject -Class Win32_OperatingSystem |
Select-Object TotalVisibleMemorySize, FreePhysicalMemory |
ForEach-Object {
[PSCustomObject]@{
'TotalMemoryMB' = [math]::Round($_.TotalVisibleMemorySize / 1024, 2)
'FreeMemoryMB' = [math]::Round($_.FreePhysicalMemory / 1024, 2)
'UsedMemoryMB' = [math]::Round(($_.TotalVisibleMemorySize - $_.FreePhysicalMemory) / 1024, 2)
}
}
Why it matters: This comprehensive snapshot is a go-to tool for on-the-fly diagnostics. Whether you’re troubleshooting performance issues, memory leaks, or high CPU usage, this command instantly reveals which processes are draining resources—without launching Task Manager or Performance Monitor. Ideal for quick triage during server slowdowns or SQL bottlenecks.
7. Check System Uptime
$uptime = (Get-Date) - (Get-CimInstance Win32_OperatingSystem).LastBootUpTime
Write-Host "System Uptime: $($uptime.Days) Days, $($uptime.Hours) Hours, $($uptime.Minutes) Minutes" -ForegroundColor Cyan
Why it matters: Quickly see how long the system has been running—helpful in determining recent reboots or crashes.
8. Check Disk Space
Get-PSDrive -PSProvider FileSystem | Select-Object Name, Used, Free, @{Name="Free(GB)";Expression={"{0:N2}" -f ($_.Free / 1GB)}}
Why it matters: Instantly assess available drive space and avoid unexpected application or SQL failures due to low disk capacity.
9. Review Event Logs (System Errors Only)
Get-EventLog -LogName System -EntryType Error -Newest 20 | Format-Table TimeGenerated, Source, EventID, Message -AutoSize
Why it matters: Check for hardware, driver, or system errors logged in the last events—critical when troubleshooting.
10. Forensic Script Scan – Local Machine Analysis
This script performs a forensic scan of the local machine, identifying recently modified files with common scripting and development extensions. It’s ideal for monitoring changes or performing audits.
$targetPath = "C:\"
$extensions = '*.ps1', '*.php', '*.sql', '*.bat', '*.cmd', '*.vbs', '*.js', '*.dll', '*.config', '*.json'
$outputPath = "C:\Temp\ScriptAuditReport.csv"
Get-ChildItem -Path $targetPath -Include $extensions -Recurse -ErrorAction SilentlyContinue |
Where-Object { $_.LastWriteTime -gt (Get-Date).AddDays(-90) } |
Sort-Object LastWriteTime -Descending |
Select-Object FullName, LastWriteTime |
Export-Csv $outputPath -NoTypeInformation
Why it matters: Use this script when you suspect undocumented code changes, malicious automation, or hidden activity on a machine. It pinpoints recently altered files with extensions commonly used for scripting or system manipulation. Ideal for incident response or auditing newly repurposed systems.
Final Thoughts
PowerShell is a must-have tool for IT professionals. These scripts help automate tasks, troubleshoot issues, and improve system efficiency. Which of these commands do you find most useful? Let me know in the comments!
🚀 Stay tuned for more PowerShell tips and tricks!
© 2012–2025 Jet Mariano. All rights reserved.
For usage terms, please see the Legal Disclaimer.